Password Hacking or Cracking has evolved over the years, with instances of serious credential-based attacks topping headlines daily. Why? It’s become frighteningly easy for cybercriminals to get your password. Several high-profile attacks in recent news (SolarWinds, The US Pipeline … and so on) sparked an executive order from the White House calling for improved cybersecurity practices in the enterprise, specifying Multi-Factor Authentication and Zero Trust security solutions.
But just how easy is it? For starters, try searching for How to Hack a Password on YouTube.
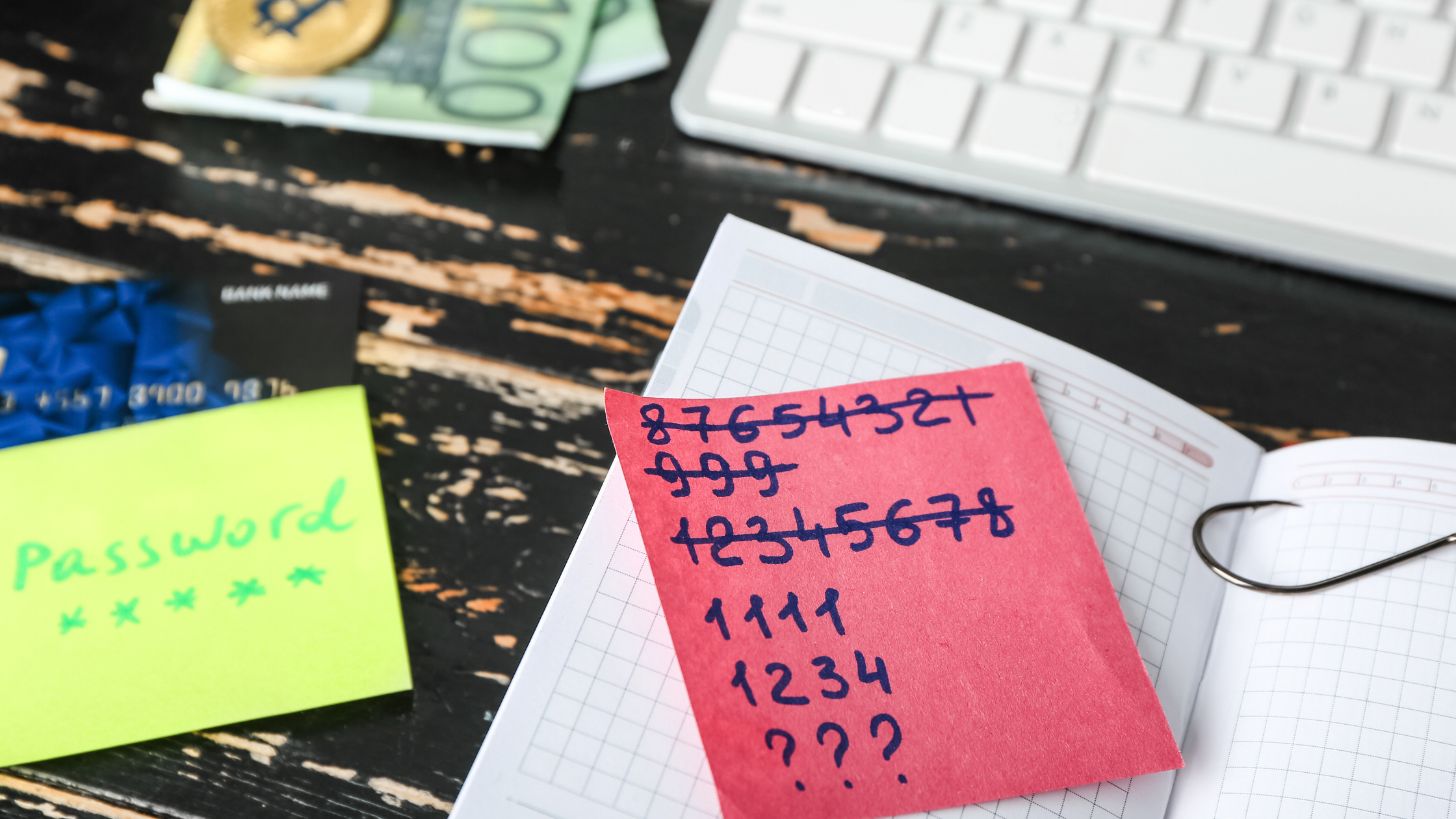
Here is our Top 10 List of hacking and cracking methods.
1. Phishing
One of the most common ways in which a bad actor can obtain your password is by asking for it! Phishing emails look like they’re coming from a legitimate source, when it’s a bad actor impersonating one in order to get you to enter information, usually your credentials. You can read more about Phishing here.
2. Dictionary Attack
The dictionary attack is a more sophisticated brute force attack that uses technology to automatically enter commonly used passwords into a computer until something works. These “dictionaries” usually contain compromised passwords from previous attacks, along with common combinations. This technique is common because people generally use easy-to-remember phrases as passwords, and then reuse them across multiple accounts.
3. Mask Attack
Mask attacks are more refined guessing, usually based on some knowledge of the victim. The attacker configures a “mask” to try only certain types of passwords with characters and numbers they know exist. Again, using technology to guess, hackers can reduce the time it takes to arrive at the right credential.
4. Rainbow Table Attack
Stored passwords are often encrypted with a ‘hash’ which makes it impossible to find an original password without the hash that goes with it. Hackers can bypass this through shared directories that record passwords (usually built from previous hacks) with their corresponding hashes. This method uses hash algorithms to reduce time to find the password-hash combination and obtain access to systems.
5. Malware
Keyloggers and screen scrapers are examples of malware that hackers install on a victim’s system in order to steal data. These are used to specifically target passwords by recording what you type, taking screenshots, or even scraping the victim’s system for password files such as those you save in your browser. (For more on why you shouldn’t let your browser store passwords read here.)
6. Offline Cracking
While one might think that their passwords should be safe as long as a system is not online, most of a hacker’s work takes place offline. Hackers know that systems usually limit the number of guesses before an account is locked.
During offline hacking, passwords can be decrypted using a list of hashes – typically from a previous data breach. This can only be done once a hacker has already gained access to an unprotected server or database.
7. Spidering
Spidering is a technique that requires some knowledge of an individual or company. For example, hackers might try to get to know a company by accessing documentation like guides, handbooks, or material that reveals things like how to access resources or which platforms and security tools the company uses. It is often the case that passwords are related to the business somehow, which makes it easier for hackers to guess – again, usually using an automated process to find the right string of characters for access.
8. Fake WAP
Perhaps one of the scariest and easiest hacks to achieve is the Fake WAP, where the attacker sets up a wireless router with a legitimate-sounding name in a public spot with the hopes people will connect to it. From there the hacker can monitor connections and access a user’s information or force the user to download malware onto their device.
9. Network Analyzers
Network analyzers allow hackers to monitor and intercept data that is sent over a network and to find the plain text passwords inside.
10. Guess!
Perhaps the most common method for password hacking is simply to guess. As most users will use a common phrase, birthday, pet name, and so on for login, hackers often have a pretty good chance. Much of that information is contained within the material on your company, or in your social media profiles, etc.
The Simple Solution? Don’t Use Them!

To find out more about how you can Go Passwordless today with TraitWare’s Passwordless MFA + SSO solution for True Zero Trust Access™ for your company, please contact us and we’ll show how in a few minutes.
We do understand that individuals are required to have passwords for access. This is why we’ve partnered with Keeper Security. If you must use a password, use a Password Manager like Keeper’s. With TraitWare, you can have passwordless access to your Keeper Vault and safely store all your credentials in one place.
1 Comment