
“Secrets to a better password and fewer hacks” published by CNBC
It goes on to talk about a machine that IBM built (the Cracken) that can crack any password up to 14 characters in 5 minutes or less.
December 3, 2018
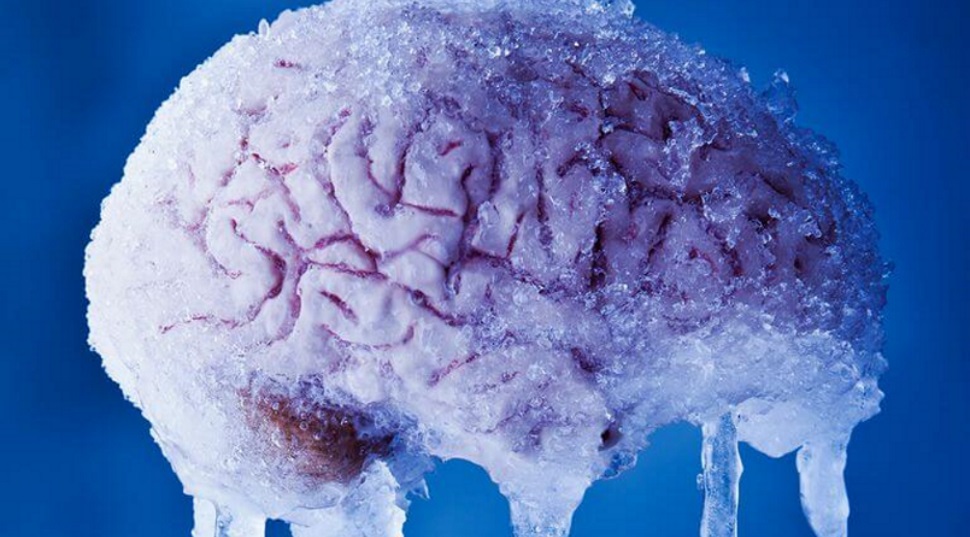
Are You Becoming Numb to Data Breaches?
Nearly every day we read about yet another data breach. They come from every market and size of company.
December 3, 2018

Secure Login News
Recently, the topic of protecting the individual (user) at the point of entry (login), to a application or digital resource has risen to the top of security discussion.
November 26, 2018

Official Sponsor WordCamp Jacksonville Fl
Interspersed with all of these conversations, you’ll want to attend many of the informative and entertaining sessions prepared by our cast of talented speakers.
November 26, 2018