
Phight the Phish with Phishing-Resistant MFA
This is something worth thinking about as cybercrime continues to grow and evolve, and as companies are looking to protect themselves and company valuables from costly attack. Cybercriminals are getting craftier with their methods. Take recent news of a Phishing attack targeting Microsoft 365 email accounts. This large-scale campaign used a relatively new method called AiTM or Adversary […]

You can’t have Security without Privacy
Privacy vs. Security. Can you have both? While there’s a difference, we think the two belong together – especially when it comes to Identity. While data security has become increasingly important for companies of all sizes – with the risk and severity of cyberattack steadily rising – regulations like GDPR, CCPA mean companies are also having […]

BACK TO SCHOOL FOR CYBERCRIME WITH TRAITWARE.
Schools are top targets for Cybercrime. It’s time to get educated and educate about the risks, and how to implement a Zero Trust framework for security. With students of all ages still in the early days of their academic year, cybersecurity experts issue stern warnings about cybercrime in schools. With the increased use of technology […]

BUSTING MYTHS: THE TRUTH ABOUT BIOMETRICS
FOR IDENTITY & ACCESS MANAGEMENT With cybercrime in today’s headlines almost daily, companies are looking to modernize security protocols. Biometrics are being widely adopted for greater security and for improved user experience. Yet some are still hesitant to make the shift. Here are a few myths about biometrics that need busting: 1. Biometric images can […]

A Paradigm Shift in IAM – The Move to Zero Trust Access
A person's identity is the first pillar in a Zero Trust framework. Achieving True Zero Trust Access requires having MFA inherent upon account creation.
Cyber Insurance Isn’t Enough to Protect You
What Companies should consider BEFORE buying Cyberattacks have risen by more than 300% since 2019 and experts predict that cybercrime will only increase in frequency and severity as attackers get smarter, more sophisticated, and more organized. Recent news has focused on larger companies – including those with government ties, which is of particular concern. But […]

Traditional MFA and Passwords are not cyber secure
People say Multi-Factor Authentication (MFA) is the answer. But your typical MFA isn't as safe as you think.
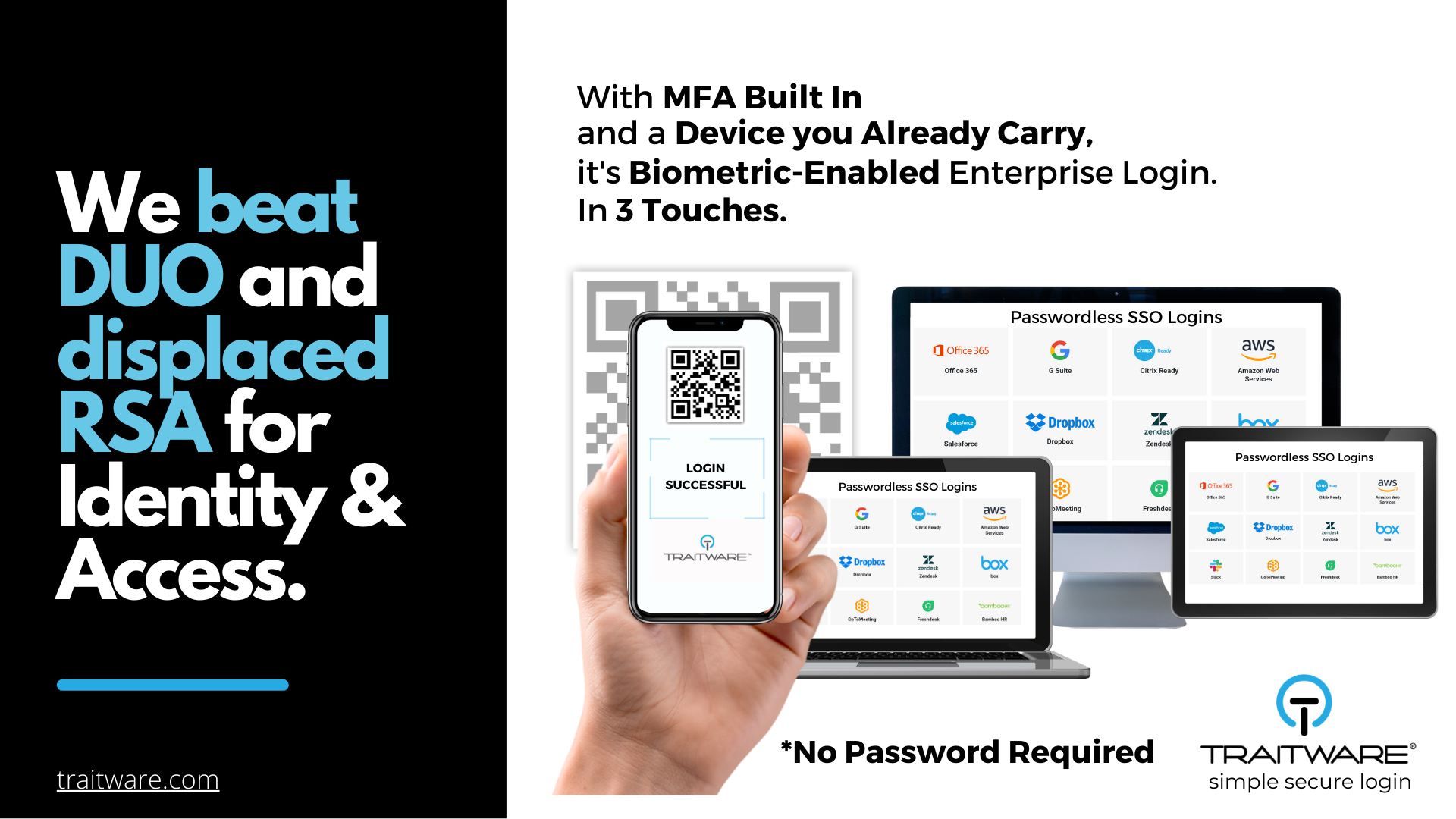
How TraitWare Passwordless MFA Beats Competition for Healthcare Security
TraitWare’s patented, plug-and-play Identity & Access solution is chosen by leading Healthcare Services Company (HSC) – beating DUO and displacing RSA – because of greater security, ease of use, and cost savings. Reno, Nevada – April 20, 2021 – TraitWare® today announced that the HSC will adopt TraitWare’s passwordless authentication technology for its employees, healthcare […]

TraitWare delivers simple, secure access to Citrix Workspace
Citrix continues to empower companies to have better and more secure access to enterprise resources. Now, it has expanded its capabilities and enhanced user experience, efficiency, and security by deploying modern authentication integrations for Citrix Workspace via SAML 2.0. What is SAML 2.0? Security Assertion Markup Language (SAML) is an XML-based open standard for transferring identity […]
IAM Configuration Mistakes Businesses Cannot Afford to Make
Identity and access management spells sound cloud security—provided that permissions are properly configured. If not, then a business is essentially risking its success, even its survival in the event of a major breach that results in loss of data, clients, and the support of stakeholders. Vital cloud services (e.g., Google IAM, Microsoft Azure Active […]

20 Identity and Access Management (IAM) Terms You Need to Know
Forget buzzwords and buzz phrases. These terms are keepers, and knowing them can go a long way to help you navigate identity and access management for your organization’s systems and networks. Access management The processes and technologies used to control and monitor network access. Access management features, such as authentication, authorization, trust and security auditing, […]

Why Access control should be a Top Security Priority?
At its most basic, access control is a means of ensuring that users who are logged in to your system are who they say they are, and that they have been granted appropriate access to your organization’s data. At a highly technical level, Daniel Crowley, head of research for IBM’s X-Force Red, describes access control […]