
Why Companies do not want to Go Passwordless
Addressing the Top 4 Reasons for Hesitation Studies have shown an increased appetite among consumers for multi-factor authentication, including biometrics as a replacement for the username and password login method, and evidence is clear that credential-based login poses the number one threat for security breaches. Experts and tech writers have been saying that we need to “break […]

20 Identity and Access Management (IAM) Terms You Need to Know
Forget buzzwords and buzz phrases. These terms are keepers, and knowing them can go a long way to help you navigate identity and access management for your organization’s systems and networks. Access management The processes and technologies used to control and monitor network access. Access management features, such as authentication, authorization, trust and security auditing, […]

Why Access control should be a Top Security Priority?
At its most basic, access control is a means of ensuring that users who are logged in to your system are who they say they are, and that they have been granted appropriate access to your organization’s data. At a highly technical level, Daniel Crowley, head of research for IBM’s X-Force Red, describes access control […]

Should Have Authentication and Authorization to be Cyber secure
How Is Authentication Different from Authorization, and Why Should You Have Both? Authentication is concerned with identity, while authorization is concerned with action. Authentication involves validating the identity of a registered user attempting to gain access to data resources such as an application, an API, or microservices. Authorization involves specifying what actions a registered user […]

Cyber Resiliency for Small Businesses: Techniques and Tips
Cyber Resiliency for Small Businesses: Techniques and Tips In the context of cybersecurity, resiliency is all about how organizations bounce back from an incident that involves the interconnection of multiple domains such as cybersecurity, business continuity, and organizational operations. You need to be cyber resilient to adapt and continue to deliver services or provide products […]
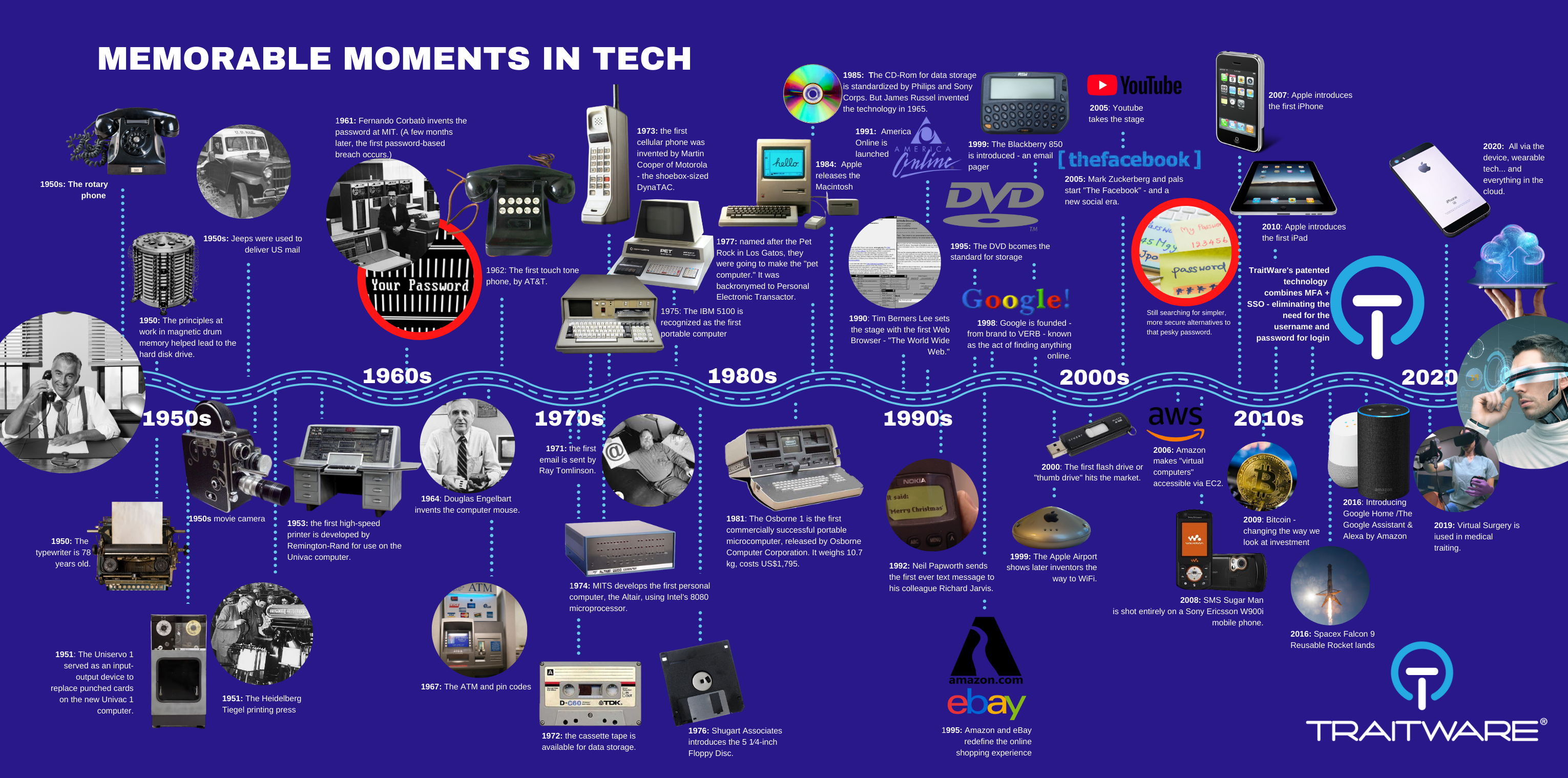
How Tech has Evolved. And How it Really Hasn’t.
It’s Time to Fix What’s Been Broken From the Get-Go As humans, we’ve evolved a fair amount. But Technology is another animal altogether. Taking a look at our infographic, the technological shifts we’ve witnessed since the 1950s are nothing short of mind-blowing. From pen and paper and a phone to today’s superpowered mobile devices, AI, […]

Beware of Tycoon – the Ransomware Targeting Windows and Linux Systems
Beware of Tycoon—the Ransomware Targeting Windows and Linux Systems. Windows and Linux systems are in the cyber-crosshairs of a recently uncovered ransomware, in what appears to be a targeted campaign. Tycoon is a multi-platform Java ransomware that is deployed in the form of a Trojanized Java Runtime Environment (JRE) and leverages an obscure Java image […]

Zero Trust, and How Does Multifactor Authentication Support It?
What Is Zero Trust, and How Does Multifactor Authentication Support It? At the 29th iteration of the RSA Conference (RSAC), one of the most well-attended yearly events for online security, discussions zeroed in on the urgency for more fresh strategies to battle threats to data security. While banking and telecommunications industries obviously have huge stakes […]

Enhance Security and User Experience with Passwordless SSO Logins
For On-Premise or Cloud-Based Resources Enhance Security and User Experience with Passwordless SSO Logins. Username and password logins are not a secure option for individuals and organizations alike as data breaches and malicious attacks get more and more sophisticated. Even the strongest passwords fail to reassure the most risk-averse users. If you’re this kind of […]

How Cybercriminals Exploit COVID-19 to Compromise Businesses’ Data Security
How Cybercriminals Exploit COVID-19 to Compromise Businesses’ Data Security. The COVID-19 pandemic is the kind of crisis that gives malicious actors increased options and opportunities, and they will not be shy about exploiting organizational and individual cybersecurity vulnerabilities. Here are 6 ways you can be targeted: 1. Phishing campaigns Cybercriminals have been taking advantage of […]
Beware of Phishing Attacks That Can Bypass 2-Factor Authentication
Phishing attacks that can bypass 2-factor authentication. Where 2FA normally offers an extra layer of protection that is lacking in single-layer protection provided by usernames and passwords. In most cases, that should give businesses some much-needed peace of mind. But hackers are forever finding ways to circumvent any security measures developed to thwart their malicious […]

How to Telecommute Securely During the COVID-19 Pandemic
The coronavirus has given businesses and organizations little to no choice but to adopt telecommuting on a bigger scale than many probably would have been happy with. Telecommuting securely during Covid 19 is a must. The massive shift in working arrangement has changed the way employees interact with company systems and data, and the transition […]